
GitHub will start requiring active developers to enable two-factor authentication (2FA) on their accounts beginning next week, on March 13.
Once expanded to the company's entire user base, the 2FA enrollment requirement will help secure the accounts of more than 100 million users.
The gradual rollout will start next week with GitHub reaching out to smaller groups of administrators and developers via email and will speed up as the end of the year approaches to ensure that onboarding is seamless and users have time to sort out any issues.
"GitHub has designed a rollout process intended to both minimize unexpected interruptions and productivity loss for users and prevent account lockouts," said Staff Product Manager Hirsch Singhal and Product Marketing Director Laura Paine.
"Groups of users will be asked to enable 2FA over time, each group selected based on the actions they've taken or the code they've contributed to."
If your account is selected for enrollment, you will receive an email and see a banner on GitHub.com requesting you to enroll in the two-factor authentication (2FA) program.
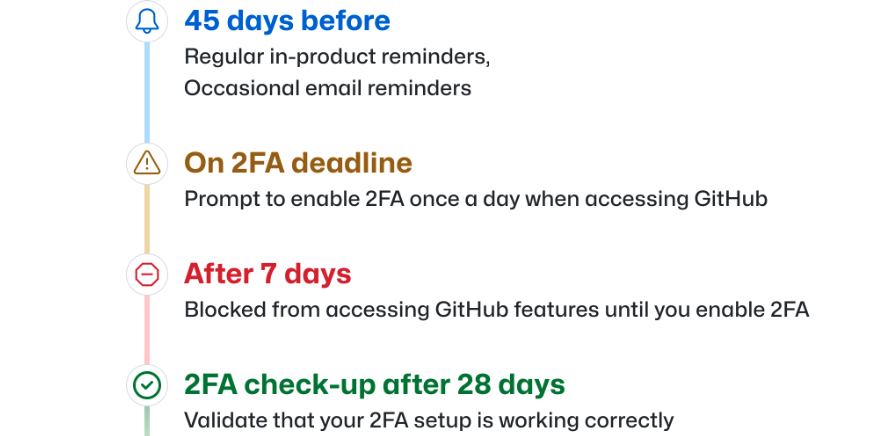
Then, you'll have 45 days to configure 2FA on your account, during which you can keep using your GitHub account as usual, except for occasional reminders.
GitHub will keep you updated on your enablement deadline, and once it has passed, you will be prompted to enable 2FA the first time you access GitHub.com and blocked from accessing some features until 2FA is toggled on.
This follows two previous announcements from May and December that all developers contributing code on the platform will be required to enable 2FA by the end of 2023.
GitHub provides detailed instructions on configuring 2FA for your account and recovering accounts when losing 2FA credentials.
Developers can use one or more 2FA options, including physical security keys, virtual security keys built into mobile devices like smartphones and laptops, Time-based One-Time Password (TOTP) authenticator apps, or the GitHub Mobile app (after configuring TOTP or SMS 2FA).
Although text message-based 2FA is also an option (in some countries), GitHub is urging users to switch to security keys or TOTP apps because threat actors can bypass SMS 2FA or steal SMS 2FA auth tokens to hijack the developers' accounts.
Securing the software supply chain
Enabling 2FA on GitHub accounts increases resilience against account takeover by blocking attempts to use reused passwords or stolen credentials in hijacking attacks.
This is the company's latest move towards securing the software supply chain by moving away from basic password-based authentication.
Previously, the code hosting platform implemented email-based device verification and phased out account passwords for Git operation authentication.
Additionally, GitHub disabled password authentication via the REST API back in November 2020 and introduced support for FIDO2 security keys to secure SSH Git operations in May 2021.
Over the years, GitHub has enhanced its account security measures by incorporating two-factor authentication, sign-in alerts, blocking the use of compromised passwords, and providing support for WebAuthn.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now