I can't tell if the Locky developers are trying to put us to sleep with all their extension changes or paying homage to the Tryptophan in Thanksgiving turkey, but they have changed the extension used for encrypted files to .zzzzz.
Early this morning, MalwareHunterTeam discovered the new Locky extension being submitted to ID-Ransomware and then security researcher Derek Knight discovered a new Locky campaign spewing out emails that pretend to be an order receipts. After installation of the attached ZIP files it was determined that Locky switched to the .zzzzz extension. It should also be noted that there are also still reports of the .aesir variant currently being distributed as well.
Unfortunately, at this time there is still no way to decrypt the Locky Ransomware.
Locky ZZZZZ variant being distributed via Fake ISP Complaint Emails
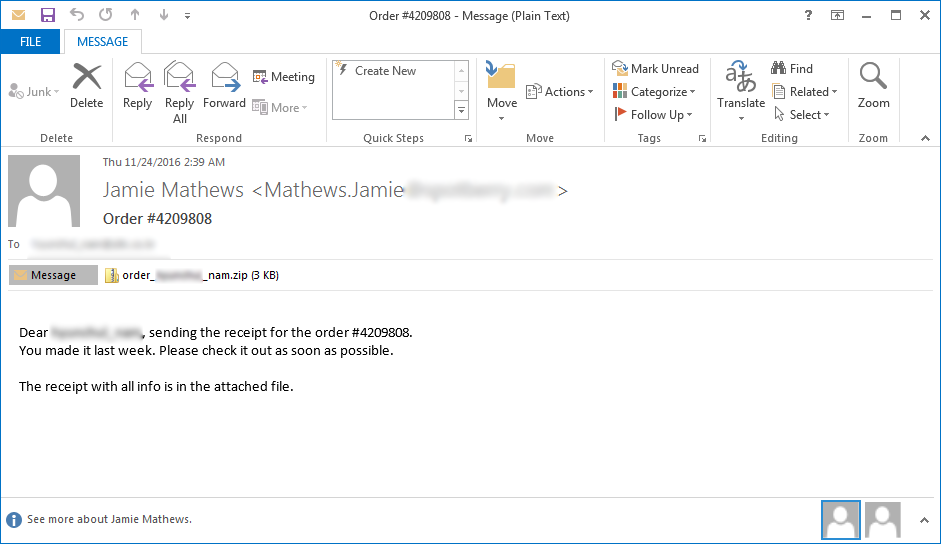
This new Locky campaign is being distributed through emails that pretend to be receipts for an order placed by the recipient. These emails will contain a subject of Order #[random_numbers] and contain a zip attachment with a name like order_[target_name].zip. Inside this ZIP file is a JS file that when opened will download and execute the Locky ransomware.
Locky installed by Renamed DLL Files
When the JS attachment is executed it will download an encrypted DLL and decrypt it into the %Temp% folder of the machine. Recently, the Locky devs have switched to downloading DLL files that are named with a non-dll extension. For example, the Locky DLL installer I had tested had an extension of TDB.
This DLL file will then be executed using the legitimate Windows program called Rundll32.exe in order to install Locky on the computer.
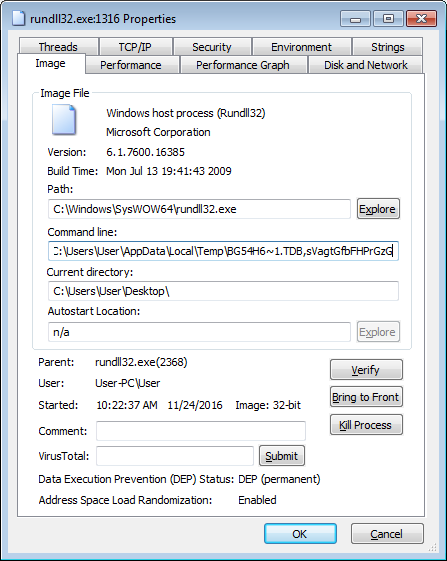
The Locky DLL is currently being executed with a command similar to the one below. Please note that the DLL name and the export being used to install Locky will not be same in all cases.
"C:\Windows\System32\rundll32.exe" %Temp%\BG54H6~1.TDB,sVagtGfbFHPrGzG
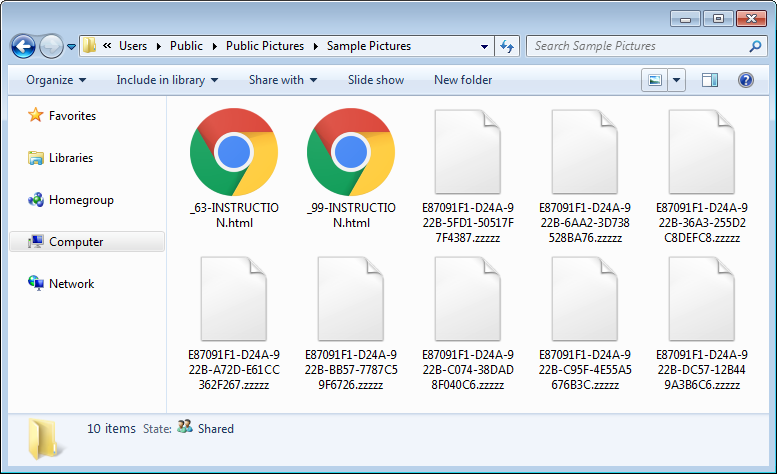
Once Locky is installed it will scan the computer for certain file types and encrypt them. When encrypting a file, it will scramble the name and append the .zzzzz exension. For example, a file called test.jpg could be renamed to 016CCB88-61B1-ACB8-8FFA-86088F811BFA.zzzzz. The format for this naming scheme is first_8_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[4_hexadecimal_chars]-[12_hexadecimal_chars].zzzzz
The currently targeted extensions are the same as the previous version:
.001, .002, .003, .004, .005, .006, .007, .008, .009, .010, .011, .123, .1cd, .3dm, .3ds, .3fr, .3g2, .3gp, .3pr, .602, .7z, .7zip, .ARC, .CSV, .DOC, .DOT, .MYD, .MYI, .NEF, .PAQ, .PPT, .RTF, .SQLITE3, .SQLITEDB, .XLS, .aac, .ab4, .accdb, .accde, .accdr, .accdt, .ach, .acr, .act, .adb, .adp, .ads, .aes, .agdl, .ai, .aiff, .ait, .al, .aoi, .apj, .apk, .arw, .asc, .asf, .asm, .asp, .aspx, .asset, .asx, .avi, .awg, .back, .backup, .backupdb, .bak, .bank, .bat, .bay, .bdb, .bgt, .bik, .bin, .bkp, .blend, .bmp, .bpw, .brd, .bsa, .cdf, .cdr, .cdr3, .cdr4, .cdr5, .cdr6, .cdrw, .cdx, .ce1, .ce2, .cer, .cfg, .cgm, .cib, .class, .cls, .cmd, .cmt, .config, .contact, .cpi, .cpp, .cr2, .craw, .crt, .crw, .cs, .csh, .csl, .csr, .css, .csv, .d3dbsp, .dac, .das, .dat, .db, .db3, .db_journal, .dbf, .dbx, .dc2, .dch, .dcr, .dcs, .ddd, .ddoc, .ddrw, .dds, .der, .des, .design, .dgc, .dif, .dip, .dit, .djv, .djvu, .dng, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .drf, .drw, .dtd, .dwg, .dxb, .dxf, .dxg, .edb, .eml, .eps, .erbsql, .erf, .exf, .fdb, .ffd, .fff, .fh, .fhd, .fla, .flac, .flf, .flv, .flvv, .forge, .fpx, .frm, .fxg, .gif, .gpg, .gray, .grey, .groups, .gry, .gz, .hbk, .hdd, .hpp, .html, .hwp, .ibank, .ibd, .ibz, .idx, .iif, .iiq, .incpas, .indd, .iwi, .jar, .java, .jnt, .jpe, .jpeg, .jpg, .js, .kc2, .kdbx, .kdc, .key, .kpdx, .kwm, .laccdb, .lay, .lay6, .lbf, .ldf, .lit, .litemod, .litesql, .log, .ltx, .lua, .m2ts, .m3u, .m4a, .m4p, .m4u, .m4v, .mapimail, .max, .mbx, .md, .mdb, .mdc, .mdf, .mef, .mfw, .mid, .mkv, .mlb, .mml, .mmw, .mny, .moneywell, .mos, .mov, .mp3, .mp4, .mpeg, .mpg, .mrw, .ms11, .ms11 (Security copy), .msg, .myd, .n64, .nd, .ndd, .ndf, .nef, .nk2, .nop, .nrw, .ns2, .ns3, .ns4, .nsd, .nsf, .nsg, .nsh, .nvram, .nwb, .nx2, .nxl, .nyf, .oab, .obj, .odb, .odc, .odf, .odg, .odm, .odp, .ods, .odt, .ogg, .oil, .onetoc2, .orf, .ost, .otg, .oth, .otp, .ots, .ott, .p12, .p7b, .p7c, .pab, .pages, .pas, .pat, .pcd, .pct, .pdb, .pdd, .pdf, .pef, .pem, .pfx, .php, .pif, .pl, .plc, .plus_muhd, .png, .pot, .potm, .potx, .ppam, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prf, .ps, .psafe3, .psd, .pspimage, .pst, .ptx, .pwm, .py, .qba, .qbb, .qbm, .qbr, .qbw, .qbx, .qby, .qcow, .qcow2, .qed, .r3d, .raf, .rar, .rat, .raw, .rb, .rdb, .re4, .rm, .rtf, .rvt, .rw2, .rwl, .rwz, .s3db, .safe, .sas7bdat, .sav, .save, .say, .sch, .sd0, .sda, .sdf, .sh, .sldm, .sldx, .slk, .sql, .sqlite, .sqlite3, .sqlitedb, .sr2, .srf, .srt, .srw, .st4, .st5, .st6, .st7, .st8, .stc, .std, .sti, .stm, .stw, .stx, .svg, .swf, .sxc, .sxd, .sxg, .sxi, .sxm, .sxw, .tar, .tar.bz2, .tbk, .tex, .tga, .tgz, .thm, .tif, .tiff, .tlg, .txt, .uop, .uot, .upk, .vb, .vbox, .vbs, .vdi, .vhd, .vhdx, .vmdk, .vmsd, .vmx, .vmxf, .vob, .wab, .wad, .wallet, .wav, .wb2, .wk1, .wks, .wma, .wmv, .wpd, .wps, .x11, .x3f, .xis, .xla, .xlam, .xlc, .xlk, .xlm, .xlr, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .ycbcra, .yuv, .zip
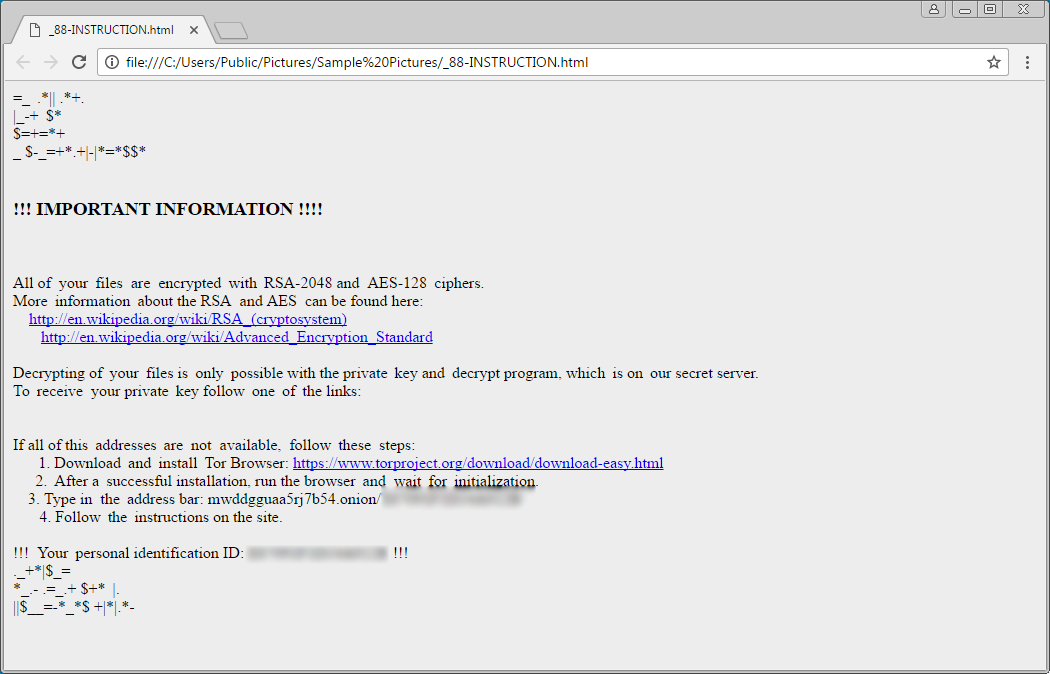
When Lock has finished encrypting the computer, it will display ransom notes that provide information on how to pay the ransom. The names of these ransom notes have changed for the ZZZZZ Locky variant and are now named _[number]-INSTRUCTION.html, -INSTRUCTION.html, and -INSTRUCTION.bmp.
It is not possible to decrypt the Locky Ransomware ZZZZZ Variant
Unfortunately, it is still not possible to decrypt .ZZZZZ files encrypted by the Locky Ransomware for free.
The only way to recover encrypted files is via a backup, or if you are incredibly lucky, through Shadow Volume Copies. Though Locky does attempt to remove Shadow Volume Copies, in rare cases ransomware infections fail to do so for whatever reason. Due to this, if you do not have a viable backup, I always suggest people try as a last resort to restore encrypted files from Shadow Volume Copies as well.



Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now